| Week 1 | T&L Activities:4.1 Legislation4.1.1 Understand the key points and implications to employers of the relevant health and safety legislation:Health and Safety at Work Act:The health and safety at work regulations that are currently in place within the UK is held in high regard globally as legislation, to the point that other countries use this legislation as a benchmark for their own. Created in 1974 the regulation was created as a result of a significant amount of harm and death related to employees undertaking their work roles and responsibilities. The government established a group of people chaired by Lord Robens to create a report on safety and health at work. Lord Robens was tasked to create legislation that fit all business types regardless of size, from self-employed to large organisations.
o key points: – provide a safe working environment – ensure staff are properly trained – adequate welfare provision – provide relevant information, instruction and supervision You have been tasked with creating an engaging activity for 16-18 year olds on the Health and Safety at Work etc Act 1974, specifically linked to the digital support services sector. This activity should last 10-15 minutes and involve both a learning element and interactive participation. You have been tasked with creating an informative presentation that includes examples and casestudies of the Health and Safety at work Act. Manual handling operations:o key points: – avoid hazardous manual handling operations as far as possible – assess any hazardous manual handling operations – provide information on load and centre of gravity – reduce the risk of injury so far as is reasonably practicable Work at height regulations:The regulations around "working at height 2005" play a very important part when linked to the installation of possible network infrastructure as placing equipment such as network access points (APs), Wi-Fi hubs and physical network cabling. These elements of a network can be located in ceilings and overhead gantries that require access to be done using ladders and in some situations scissor lifts called cherry pickers. As a result, the legislation is designed to ensure that employees are protected when undertaking any activities associated to accessing this equipment. The legislation requires that any employer ensure appropriate precautions are in place to reduce any possible injury, such as falling from height. The Legislation and regulation ensure that the employee understands their duty to protect its employees by; Ensuring that the equipment they are using or provided with is suitable for the job being undertaken, that it is strong enough for the task in hand, and that it is regularly checked for integrity and maintenance. Appropriate training has been provided to ensure that the employees don't act in a way that could lead to harm to them or others, such as overreaching. Provide the employees and potential members of the public with protection that reduces their being hit by falling materials. Identifying Work at Height Risks in a Digital Support Environment o key points: – make sure the work is properly planned, supervised and carried out by competent people – do as much work as possible from the ground – ensure workers can get safely to and from where they work at height – ensure equipment is suitable, stable and strong enough for the job – provide protection from falling objects – consider emergency evacuation rescue procedures
Display screen equipment:o implications to employers: – conduct a display screen equipment workstation assessment – reduce risks including making sure workers take breaks from display screen equipment work – provide an eye test if an employee asks for one – provide training and information for employees. Have you ever had neck pain after a long gaming session or after doing work on a computer, or, found that your eyes have gotten tired and sore after looking at screens all day? This is where the Health and Safety (Display Screen Equipment) Regulations 1992 come in. This regulation is designed to protect users who continually use display screens for a long period. Some of the key principles of the regulations to keep you safe when using computers, laptops, and tablets for extended periods are:
5-Minute Challenge: In Pairs assess your computer setup for 5 minutes. Here's what to check: Now that you have reflected on your own work areas use the government checklist (provided using the button below) to see what is expected of an employer for thier employees. Create a poster that uses terminology and images that a 16 year old might use to inform them of the DSE legislation of 1992. Using images in your poster will support your information and explainations, ensure that any images are referenced and attributed. 4.1.2 Understand the health and safety risks and preventative measures of working with digital systems:Possible risksUsing display screen equipment Musculoskeletal Disorders (MSDs): Poor posture and a poorly designed workstation can cause pain and disorders in the neck, shoulders, back, arms, wrists, and hands. This includes conditions such as repetitive strain injury (RSI). Eye Strain and Visual Problems: Extended screen use can cause tired eyes, discomfort, temporary blurred vision, dry eyes, and headaches, a condition known as Computer Vision Syndrome (CVS). It does not cause permanent eye damage but can highlight pre-existing vision problems. Fatigue and Stress: Long periods of static work, intense concentration, or poorly designed software/work organisation can lead to general physical and mental fatigue, and stress.
Working at heights Falls from height: Distraction caused by looking at a screen or interacting with a digital device (tablet, phone, laptop) can lead to a loss of balance, misstep, or a failure to notice an edge or opening, resulting in a fall. Falling objects: Digital devices and their accessories (batteries, styluses) can be dropped, posing a serious injury risk to people and damage to equipment below. Manual handling issues: Carrying digital devices, especially with accessories (stands, spare batteries, etc.), to and from elevated work areas can increase manual handling strain, particularly if safe access is limited
Cable installation (ground level, onto walls) Electric Shock and Burns: The primary hazard from contact with live wires or damaged cables, which can cause severe injury or death. Arc Flash and Explosions: Damage to underground or in-wall cables can cause an explosion and intense flash, leading to severe burns. Slips, Trips, and Falls: Trailing cables at ground level are a significant tripping hazard in the workplace, leading to potential injuries, additional to working at any height on a ladder. Mechanical Damage: Cables are vulnerable to damage from sharp objects, crushing, or excessive pulling/bending during installation, which can compromise their integrity and create electrical or fire hazards. Fire Hazards: Faulty wiring, overloaded circuits, or damaged equipment can lead to fires. Ergonomic Risks: Improper manual handling of heavy cable spools can lead to musculoskeletal injuries. Eye Injuries: Fiber optic cables pose a risk of eye injury from the light they carry, requiring appropriate eye protection.
Manual handling Musculoskeletal Disorders (MSDs): The primary risk is developing MSDs, which include pain and disorders in the neck, shoulders, back, arms, wrists, and hands. Work-Related Upper Limb Disorders (WRULDs) / Repetitive Strain Injury (RSI): Prolonged, uninterrupted work with a keyboard and mouse, or use of handheld devices (like PDAs and smartphones) with poor posture, can lead to these overuse injuries. Back Pain: Incorrect seating, inadequate back support, and improper lifting techniques are major causes of chronic back pain. Fatigue: Maintaining the same position for extended periods, or working with excessive workloads, can cause muscle fatigue and strain. Injuries from Transporting Equipment: Carrying heavy or unbalanced loads (e.g., a laptop in a single-shoulder bag) can strain muscles and joints. Accidents: Obstructions in the work area, poor lighting, or unstable flooring when moving equipment can lead to trips, slips, and falls. Health and safety requirements
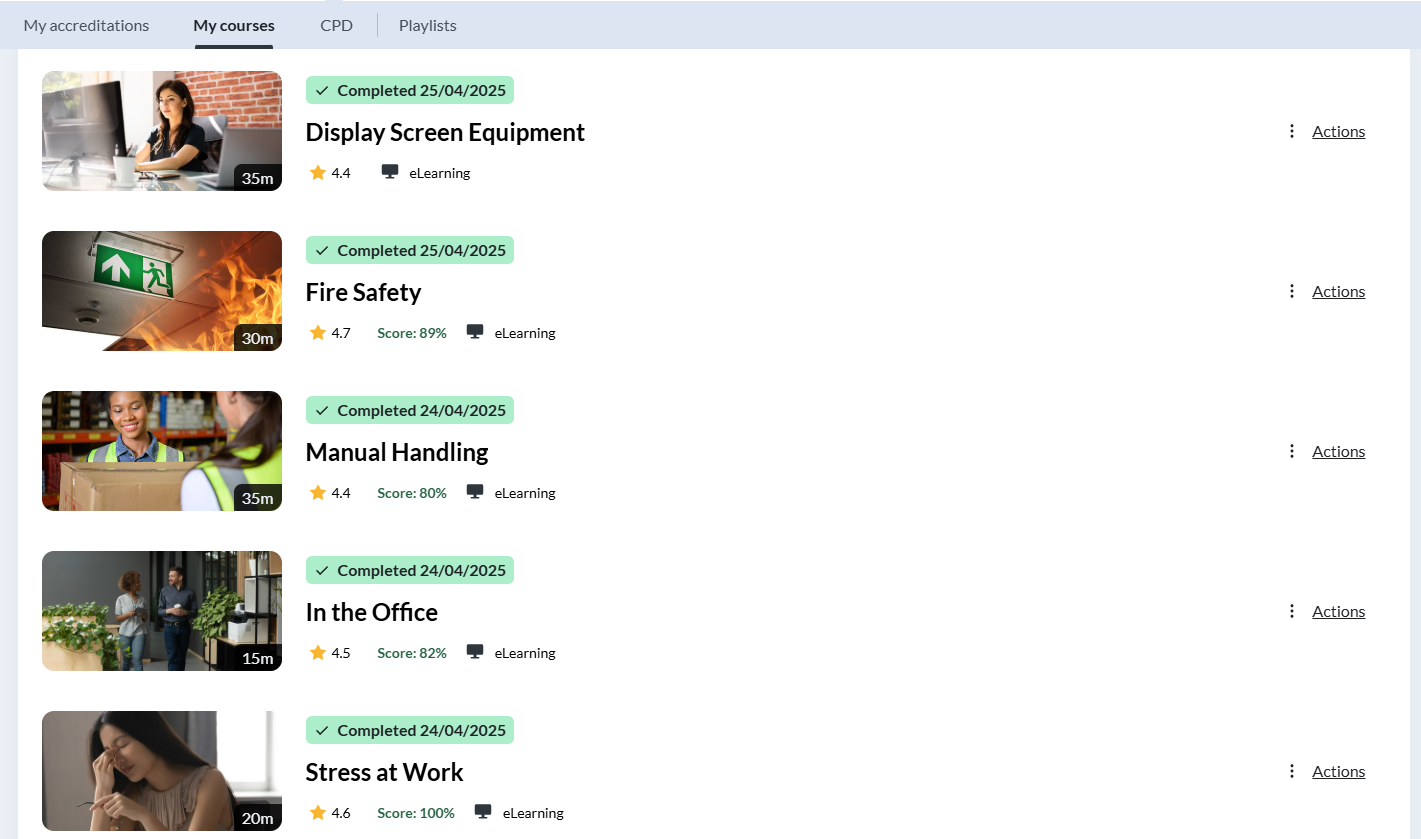
Methods of mitigating risk:Adequate training For any organisation, it is vital to ensure that the workforce has the appropriate training, skills, and knowledge to carry out their duties and responsibilities effectively, competently, and most importantly, safely. Adequate training helps to reduce the risk of human error, ensures compliance with organisational policies and legal requirements, and supports a consistent standard of working practice across the organisation. Many organisations now utilise e-learning platforms as a primary method of delivering training and sharing essential knowledge with employees. E-learning enables staff to access training materials at a time and pace that suits their individual learning needs, promoting flexibility and inclusivity within the workforce. In addition, digital training platforms allow organisations to deliver consistent, up-to-date content, track learner progress, and maintain accurate records of completed training for audit and compliance purposes. This approach not only supports ongoing professional development but also contributes to improved efficiency, reduced training costs, and a safer working environment.
Safe working environment
Suitable provision of relevant safety equipment
Safe working practices
Suitable provision of relevant information, instruction and supervision.
4.1.3 Understand Data Security and Protection legislation, including their effect on organisations and individuals:Data Protection Act/General Data Protection Regulations:Purpose of legislation Data protection legislation sets out clear rules that govern how organisations collect, use, store, share, and dispose of personal information. This applies to a wide range of organisations, including private businesses, public sector bodies, and government departments. The legislation is designed to ensure that personal data is handled lawfully, fairly, and securely, protecting individuals from misuse, unauthorised access, and excessive data collection, while also giving people greater control over how their information is processed and shared. Eight principles. 1. Lawfulness, Fairness and Transparency Personal data must be processed:
Example (Digital Support):
2. Purpose Limitation Personal data must be:
Example:
3. Data Minimisation Only data that is:
should be collected. Example:
4. Accuracy Personal data must be:
Example:
5. Storage Limitation Data must:
Example:
6. Integrity and Confidentiality (Security) Personal data must be processed securely, protecting it from:
This includes technical and organisational security measures. Examples:
7. Accountability Organisations must:
Examples:
8. Rights of the Data Subject Individuals have rights over their personal data, including:
Example: 4.1.4 Understand Computer Misuse legislation:The computer Misuse act was introduced in 1990, however it was partially introduced in 1988 in response to a legal case titled "R v Gold & Schifreen (1988) where a journalist hacker broke into the then Duke of Edinburgh’s (Prince Phillip) email account. Once the general public were aware of the situation there was outcry that uncovered the fact that no law existed against computer hacking. As a result of this the legislation was created partially and released in 1988 followed 2 years later with the full release.
How easy is it to get caught out? Refelect on your own use of digital devices, have you experienced this?
The principles of the Computer Misuse Act (CMA) 1990Key aspects of the feature governing unauthorized access include: Prohibition of Unauthorised Access: The Act clearly defines unauthorised access as accessing computer systems, programs, or data without proper authorisation. This includes bypassing security measures or accessing areas of a computer system beyond one's authorised privileges.
Protection of Data: The legislation aims to protect the confidentiality, integrity, and availability of data by preventing unauthorised access. This helps safeguard sensitive information from being accessed, modified, or deleted without proper authorisation.Scope: The legislation applies to unauthorised access to any computer system, whether it's owned by individuals, businesses, or the government. It covers a wide range of devices and networks, including computers, servers, and online platforms. • consequences for company and employee Penalties: The Act establishes penalties for unauthorized access, including fines and imprisonment, depending on the severity of the offense. For example, accessing a computer system without authorisation with the intent to commit further offenses carries a maximum penalty of up to 2 years in prison and/or a fine. • employee awareness • types of crimes covered by legislation. Secure Your Digital Vault Files that support this week | English:
|
Assessment:
|
Learning Outcomes:
|
Awarding Organisation Criteria:
|
||||||||||||||||||||||||
| Maths:
|
|||||||||||||||||||||||||||||
| Stretch and Challenge:
|
E&D / BV | ||||||||||||||||||||||||||||
| Homework / Extension:
|
ILT | ||||||||||||||||||||||||||||
| → | → | → | → | → | → | ||||||||||||||||||||||||
| Week 2 | T&L Activities:
4.1.5 Understand Equality legislation:The nine protected characteristicsThe Equality act of 2010 was bought about by the imalgimation of a number of anti-discrimination laws and legislations in 2010. The act identifies nine principles and chararcters that are protected, these are. 1. AgeProtection against discrimination based on a person’s age or age group (young or old) means that individuals must be treated fairly and equally regardless of how old they are, whether they are younger or older than the average person in a particular setting. Under UK equality legislation, it is unlawful to disadvantage someone simply because of assumptions, stereotypes, or generalisations linked to their age. This protection applies across employment, education, training, and the provision of goods and services. Decisions such as recruitment, promotion, access to training, pay, redundancy selection, and dismissal must be based on ability, competence, experience, and performance, not age. Age discrimination can take several forms:
In practice, this means employers and organisations must:
Failure to uphold age protection can lead to employment tribunal claims, compensation awards, reputational damage, and loss of skilled or experienced individuals, all of which can negatively affect organisational performance and workplace culture. In practice (compliant)
Not followed (non-compliant)
Consequences for organisations
2. DisabilityA physical or mental impairment that has a substantial and long-term negative effect on day-to-day activities refers to the legal definition of a disability under UK equality legislation. This protection ensures that individuals are not treated less favourably because of a disability and are supported to participate fully in work, education, and society. A condition is considered a disability when:
This protection covers both visible and non-visible (hidden) disabilities, including conditions such as dyslexia, autism, diabetes, epilepsy, and long-term mental health conditions. Disability discrimination can occur in several ways:
In practice, organisations have a legal duty to make reasonable adjustments to remove barriers that disadvantage disabled individuals. This may include:
Failure to support disabled individuals or make reasonable adjustments can result in employment tribunal claims, significant financial compensation, enforcement action by regulators, and serious reputational damage. Organisations that proactively support disability inclusion benefit from improved staff wellbeing, higher retention, and a more diverse and effective workforce.
In practice (compliant)
Not followed (non-compliant)
Consequences for organisations
3. Gender ReassignmentProtection for people who are transitioning, have transitioned, or identify as transgender means that individuals must not be discriminated against because of their gender reassignment status. Under UK equality legislation, a person is protected if they are proposing to undergo, are undergoing, or have undergone a process to reassign their sex, and this protection applies regardless of whether medical treatment or surgery is involved. This protection recognises that gender reassignment is a deeply personal process and that individuals have the right to be treated with dignity, respect, and privacy in all areas of life, including employment, education, and access to services. Discrimination related to gender reassignment can take several forms:
In practice, organisations are expected to:
Failure to uphold protections for transgender individuals can result in legal claims, compensation awards, and significant reputational damage. It can also lead to a toxic workplace culture, reduced staff wellbeing, and higher turnover. Organisations that actively support gender identity inclusion benefit from stronger trust, improved morale, and a more inclusive and respectful environment for all. In practice (compliant)
Not followed (non-compliant)
Consequences for organisations
4. Marriage and Civil PartnershipProtection for people who are married or in a civil partnership (employment-related only) means that employees and job applicants must not be treated less favourably because they are legally married or in a civil partnership. Under UK equality legislation, this protection applies specifically within employment and workplace contexts, such as recruitment, promotion, pay, training, and dismissal. This characteristic recognises that an individual’s legal relationship status should have no bearing on their ability to perform a role or access workplace opportunities. It applies equally to opposite-sex marriages and same-sex civil partnerships. Discrimination related to marriage or civil partnership may include:
In practice, employers must:
Failure to comply with this protection can result in employment tribunal claims, financial compensation, and damage to organisational reputation. It can also negatively affect staff morale and trust. Organisations that apply fair and inclusive practices create a more respectful working environment and benefit from higher employee engagement and retention. In practice (compliant)
Not followed (non-compliant)
Consequences for organisations
5. Pregnancy and MaternityProtection during pregnancy and maternity leave means that individuals must not be treated unfairly because they are pregnant, have recently given birth, or are on maternity leave. Under UK equality legislation, pregnancy and maternity is a protected characteristic that ensures individuals are supported during this period and are able to return to work without disadvantage. This protection applies from the start of pregnancy through to the end of statutory maternity leave and covers all aspects of employment, including recruitment, pay, promotion, training, redundancy, and dismissal. Discrimination related to pregnancy and maternity can include:
In practice, employers are required to:
Failure to uphold pregnancy and maternity protections can lead to automatic unfair dismissal claims, significant financial compensation, and serious reputational damage. It can also undermine workplace trust and staff wellbeing. Organisations that actively support pregnant employees and new parents benefit from higher staff retention, improved morale, and a positive organisational culture. In practice (compliant)
Not followed (non-compliant)
Consequences for organisations
6. RaceIncludes colour, nationality, ethnic or national origin refers to the protected characteristic of race under UK equality legislation. This protection ensures that individuals are not discriminated against, harassed, or victimised because of their racial background or heritage, and that everyone is treated fairly and with respect. Race protection covers a wide range of characteristics, including:
This protection applies across employment, education, housing, healthcare, and access to goods and services. Race discrimination can take several forms:
In practice, organisations are expected to:
Failure to comply with race protection can result in serious legal consequences, including employment tribunal claims, large compensation awards, and intervention by regulatory bodies. It can also cause significant reputational damage, loss of public confidence, and reduced staff morale. Organisations that actively promote racial equality benefit from a more inclusive culture, improved decision-making, and stronger relationships with employees and service users. In practice (compliant)
Not followed (non-compliant)
Consequences for organisations
7. Religion or BeliefIncludes religious beliefs, philosophical beliefs, or lack of belief refers to the protected characteristic of religion or belief under UK equality legislation. This protection ensures that individuals are not treated unfairly because of what they believe, how they practise their beliefs, or because they do not hold any religious or philosophical belief. This protection covers:
Religion or belief discrimination can take several forms:
In practice, organisations should:
Failure to respect religion or belief protections can lead to employment tribunal claims, financial compensation, and reputational harm. It may also create a divisive or hostile environment, reducing staff engagement and wellbeing. Organisations that actively respect religious diversity benefit from a more inclusive workplace and stronger relationships with employees and service users. In practice (compliant)
Not followed (non-compliant)
Consequences for organisations
8. SexProtection against discrimination based on being male or female refers to the protected characteristic of sex under UK equality legislation. This protection ensures that individuals are treated fairly and equally regardless of whether they are male or female, and that decisions are based on ability, merit, and performance rather than gender-based assumptions or stereotypes. This protection applies across employment, education, training, and the provision of goods and services. Sex discrimination can take several forms:
In practice, organisations must:
Failure to comply with sex discrimination protections can result in employment tribunal claims, equal pay disputes, substantial financial penalties, and serious reputational damage. It can also negatively affect organisational culture, leading to reduced morale and trust. Organisations that promote gender equality benefit from improved staff engagement, better decision-making, and a more inclusive and productive workplace. In practice (compliant)
Not followed (non-compliant)
Consequences for organisations
9. Sexual OrientationProtection for lesbian, gay, bisexual, and heterosexual individuals refers to the protected characteristic of sexual orientation under UK equality legislation. This protection ensures that individuals are not treated unfairly, harassed, or excluded because of who they are attracted to, who they form relationships with, or how they identify their sexual orientation. Sexual orientation protection applies equally to:
It covers all stages of employment and service provision, including recruitment, promotion, training, dismissal, education, and access to goods and services. Discrimination related to sexual orientation can take several forms:
In practice, organisations are expected to:
Failure to uphold sexual orientation protections can result in employment tribunal claims, financial compensation, and serious reputational damage. It can also lead to a hostile workplace culture, reduced staff wellbeing, and higher staff turnover. Organisations that actively promote inclusionand equality benefit from increased trust, stronger teamwork, and a more positive organisational reputation.
In practice (compliant)
Not followed (non-compliant)
Consequences for organisations
Further guidance is provided to organisations through a number of governmental webpages.
Equality in the Workplace – Protected Characteristics Presentation
Types of discrimination:
Direct Discrimination Definition This type of discrimination is intentional and often easy to identify because the unfair treatment is clearly linked to who the person is. Workplace Example Case Study: Pregnancy Discrimination Indirect Discrimination Definition Importantly, this discrimination is often unintentional. Workplace Example Case Study: Working Hours Policy Harassment Definition It can be:
Workplace Example Case Study: Racial Harassment at Work Victimisation Definition This includes:
Workplace Example Case Study: Retaliation After Complaint Create an infographic on the different types of descrimination that occur, Provide examples of where this has happened and the consiquences to orgnisations and individuals. Your inforgraphic should be as informative as is possible including images that capture the attention of others.
• where individuals are protected
• when to take action against discrimination o time limits for claims.
4.1.6 Understand Intellectual Property legislation:"Its all Mine, or is it? • unregistered designs • registered designs • patents. US vs China over IP
“Who Owns It?”
4.1.7 Understand Electrical Waste legislation:
The WEEE regulations are a set of environmental regulations that are designed to ensure that any electrical equipment is recycled, reused, or disposed of in an ethical and non-environmentally impacting way. Within companies, any electrical material or devices are in most situations, disposed of in specialist bins that external contractors will take away and do the recycling of the materials if they cannot be reused again, however, in some situations, some of the electrical devices may need to be destroyed beyond any repair or reuse as these may store personal and sensitive information, and must be disposed of destructively. WEEE legislation is necessary because electrical equipment contains toxic materials, such as lead and mercury, which can cause environmental damage if disposed of incorrectly. In addition, most IT equipment stores personal or organisational data, meaning unsafe disposal can lead to data breaches and security incidents. Under WEEE, organisations are required to use authorised disposal routes and ensure equipment is recycled or treated safely. Consider what mineral resources are used in most electronic devices, how are these found/collected/created? what environmental impact does the gathering of these resources have on the globe? The following video shows, the poppular TV show Gold Rush and the efforts of miners to get as much gold as they can mine. Reflect on the images in the video and the equipment that is used and the materials that these use to get to the gold. Now we should think, what electronics we have in our cupboards and draws that we no longer use. What would be done with these? In small groups of 2-3 reflect on the disposal of electrical equipment, research and discuss the main minerals found in most electrical devices and the current issue of e-waste in the UK. o key features: governs the safe and environmentally responsible disposal of electrical equipment What the Legislation says Waste Electrical and Electronic Equipment RegulationsA medium-sized UK financial services company undertook a routine IT refresh, replacing over 120 desktop PCs, laptops, and network switches. Due to time pressure and a lack of clear internal procedures, the organisation instructed facilities staff to remove the old equipment. The devices were collected by a general waste contractor, not a licensed WEEE disposal provider.
Safe disposal
Environmentally responsible disposal.Environmentally responsible disposal is the process of getting rid of waste, particularly electrical and electronic equipment (WEEE), in a way that minimises harm to the environment and protects human health while fully complying with UK environmental legislation. Electrical equipment often contains hazardous substances such as heavy metals and chemicals, which can cause serious environmental damage if released into soil or water. Environmentally responsible disposal ensures these materials are handled safely and prevents pollution and long-term ecological harm. Rather than disposing of electrical items in landfill, environmentally responsible disposal focuses on reuse, recycling, and safe treatment of waste through approved methods. Equipment that is still functional may be refurbished and reused, extending its lifespan and reducing the demand for new raw materials. Where reuse is not possible, devices are dismantled so that valuable materials such as copper, aluminium, and plastics can be recovered and recycled. Any hazardous components are removed and treated in specialist facilities. This process is carried out by licensed and authorised waste contractors who follow strict regulations and provide documentation such as waste transfer notes to demonstrate compliance. By using approved disposal routes, organisations reduce their legal risk, support sustainability objectives, and demonstrate ethical and professional practice. Overall, environmentally responsible disposal plays a vital role in protecting the environment, supporting the circular economy, and ensuring organisations meet their legal and social responsibilities. UK Organisations That Provide Environmentally Responsible Disposal Veolia Veolia is one of the UK’s largest waste management companies and provides WEEE-compliant recycling services for businesses and public sector organisations. Services include:
Biffa Biffa offers environmentally responsible WEEE disposal and works closely with organisations to reduce landfill waste. Services include:
Recycling Lives Recycling Lives focuses on ethical recycling and reuse, particularly for IT and electronic equipment. Services include:
Computer Disposals Ltd A specialist IT asset disposal (ITAD) provider that combines secure data destruction with environmentally responsible recycling. Services include:
Benefits of Using Environmentally Responsible Disposal Organisations Environmental benefits Reduces landfill waste and pollution Legal and compliance benefits Ensures compliance with WEEE Regulations Professional and reputational benefits Demonstrates corporate social responsibility Operational benefits Clear processes and expert handling Drawbacks of Using Specialist Disposal Organisations Cost Specialist WEEE and IT disposal services can be more expensive than general waste collection Administrative overhead Requires contracts, scheduling, and record-keeping Logistics Collection times may need to be booked in advance Limited control Disposal is handled externally, meaning organisations must trust third-party providers
Although environmentally responsible disposal organisations can involve higher costs and increased administration, these drawbacks are outweighed by the legal protection, environmental benefits, and reduced security risk they provide. Using licensed WEEE providers ensures compliance with legislation, protects sensitive data, and supports sustainability objectives. For organisations handling IT equipment, environmentally responsible disposal should be viewed not as an optional expense, but as a necessary part of professional and ethical practice.
To Dispose or not Dispose That is the question
4.1.8 Understand the interrelationships between digital support and securityand digital legislation, and make judgements about the impact on organisations, society and individuals.
4.1.9 Know that international law applies to some offences:• international law in cyberspace • international law and surveillance. Files that support this week | English:
|
Assessment:
|
Learning Outcomes:
|
Awarding Organisation Criteria:
|
||||||||||||||||||||||||
| Maths:
|
|||||||||||||||||||||||||||||
| Stretch and Challenge:
|
E&D / BV | ||||||||||||||||||||||||||||
| Homework / Extension:
|
ILT | ||||||||||||||||||||||||||||
| → | → | → | → | → | → | ||||||||||||||||||||||||
| Week 3 | T&L Activities:4.2 Guidelines4.2.1 Know the sources of codes of conduct:Organisations
ProfessionalBritish Computer Society (BCS)
The BCS code of conduct has four key principles,
These condes act as powerfull endorsements of individuals integrity and ethics whilst working as IT professionals. "Know IT yourself"
The Institution of Analysts and Programmers (IAP)
The Institution of Analysts and Programmers (IAP) is a professional body that supports both the public and its members by helping individuals enter the IT profession, providing technical expertise, and promoting high standards in software development. The IAP offers guidance on IT careers, particularly in systems analysis and programming, and advises on relevant training courses and qualifications, including recommending approved courses delivered by partner universities and private training providers, many of which contribute towards IAP membership or allow direct entry as a Graduate member (GradIAP). In addition, the IAP provides technical assistance through its members, who work across all areas of business and industry and may be available for consultancy, with verified credentials listed in the Register of Consultants. The organisation also supports employers, clients, and the public by confirming members’ qualifications and membership grades. Alongside this, the IAP fosters Communities of Practice (COPs) focused on improving software for society, bringing together professionals with shared interests in areas such as cyber security, health, transport, cloud computing, artificial intelligence, robotics, IoT, defence, telecoms, and software development, helping to encourage collaboration, knowledge sharing, and professional development across the IT sector. The IAP Code of Conduct covers 4 areas these are; - Duty to the Public - Duty to the Profession - Duties to the Institution of Analysts and Programmers - Duties to Clients and Employers "Investigate And Present (IAP)"
Chartered Institute of Information Security (CIISec)
The Chartered Institute of Information Security (CIISec) is the world’s first cyber and information security body to receive Royal Charter status, highlighting its leadership in raising professional standards across the sector. It operates as an independent, not-for-profit organisation governed by its members and provides a trusted, central voice for the cyber and information security profession. Representing over 35,000 professionals at all stages of their careers, CIISec supports its community through programmes focused on professional development, recognition and career success. Its core objectives include promoting the advancement and sharing of knowledge for the public benefit, establishing and upholding high ethical and professional standards in the UK and internationally, and acting as an authoritative body for consultation and research on education and issues of public interest within cyber and information security. THe CIISec has 3 areas of conduct, - Maintain Professionalism - Act in an Ethical Manner - Promote Best Practice "Investigate And Present (IAP)"
Governmental.Governmental codes of conduct and professional behaviour standards originate from:
In digital support and IT roles, aligning codes of conduct with these governmental sources ensures lawful, ethical and high-quality professional practice. The focus in these bodies is to minimises risk to the public, to protect rights and freedoms of those linked to practices and contact with services that are offered by organisation ensuring that competence and accountability is kept so that organisations maintain integrity and trust.
4.2.2 Understand how guidelines in codes of conduct influence professionalProfessional codes of conduct provide structured guidelines that shape behaviour in the workplace. They act as a bridge between organisational policies, legal requirements and day-to-day professional practice. By setting clear expectations, codes of conduct ensure individuals operate within defined standards, protecting both the public and the organisation. In sectors such as IT, cybersecurity and digital support services, professional conduct is often guided by organisations such as Chartered Institute for IT and Chartered Institute of Information Security, whose codes emphasise lawful practice, competence, integrity and responsibility. This ensures quality of work by:
BehaviourMeeting DeadlinesCodes of conduct often require professionals to act diligently and responsibly. This includes managing time effectively and delivering work within agreed timescales. How Guidelines Influence Behaviour
Linked Example An IT support technician is tasked with deploying a software security patch across a school network. The organisation’s policy requires testing before full rollout. If the technician rushes the process to meet a deadline without testing, it could:
By following procedures properly:
This approach minimises risk to users and ensures the technician demonstrates competence and integrity. Meeting deadlines is important, but meeting them professionally without bypassing safeguards is what ensures quality. Acting with Competence and IntegrityCodes of conduct require individuals to:
Example If an IT professional is asked to configure a firewall but lacks sufficient knowledge, acting with integrity means:
This ensures:
Competence ensures quality; integrity ensures ethical decision-making. • meeting deadlines • effective communication Maintaining Confidentiality and TrustConfidentiality is central to most professional codes of conduct, particularly in digital and data-driven environments. How Guidelines Influence Behaviour, Professionals must:
Linked Example A digital support technician has access to staff and student personal data stored on a management system. The code of conduct requires:
If confidentiality is breached:
By adhering to professional standards and legislation such as the Data Protection Act, the technician ensures:
Trust is fundamental in professional relationships. Without it, systems cannot function effectively. Files that support this week | English:
|
Assessment:
|
Learning Outcomes:
|
Awarding Organisation Criteria:
|
||||||||||||||||||||||||
| Maths:
|
|||||||||||||||||||||||||||||
| Stretch and Challenge:
|
E&D / BV | ||||||||||||||||||||||||||||
| Homework / Extension:
|
ILT | ||||||||||||||||||||||||||||
| → | → | → | → | → | → | ||||||||||||||||||||||||
| Week 4 | T&L Activities:
4.2.3 Know the sources of digital industry standards:International Organization for Standardization (ISO)The International Organization for Standardization (ISO) is an independent, non-governmental international organisation that develops and publishes global standards. It was founded in 1947 and is made up of national standards bodies from over 160 countries. In the UK, the national member body representing ISO is the British Standards Institution (BSI). ISO creates agreed standards to ensure that products, services, and systems are:
The main purposes of ISO are: To Ensure Quality and Consistency ISO standards provide agreed frameworks so that organisations can deliver products and services that meet customer and regulatory requirements. To Improve Safety Standards help reduce risk, protect consumers, and ensure safe working practices. To Support International Trade By using globally recognised standards, companies can trade internationally without needing to meet different technical requirements for each country. To Promote Best Practice ISO standards are built using expert knowledge from industry professionals, ensuring organisations follow proven and effective methods.
Some widely recognised ISO standards include: ISO 27001ISO 27001 is an internationally recognised standard for establishing, implementing, maintaining and continually improving an Information Security Management System (ISMS). Its purpose is to help organisations systematically protect sensitive information, including customer data, financial records and intellectual property. The standard is built around risk management: organisations must identify information assets, assess threats and vulnerabilities, evaluate risk levels, and apply appropriate security controls from Annex A (such as access control, encryption, incident response and supplier security). It follows a continual improvement model (Plan-Do-Check-Act), requiring regular monitoring, internal audits and management reviews. Certification demonstrates that an organisation has structured, documented and independently verified information security processes, which is particularly important in digital support, cybersecurity and data protection environments where confidentiality, integrity and availability must be maintained.
ISO 9001ISO 9001 is the world’s most widely adopted Quality Management System (QMS) standard. It focuses on ensuring that organisations consistently meet customer and regulatory requirements while continually improving their processes. The standard emphasises customer satisfaction, leadership commitment, process control, evidence-based decision-making and risk-based thinking. Organisations must document procedures, monitor performance, address non-conformities, and implement corrective actions where issues arise. ISO 9001 does not specify how a product or service must be delivered; instead, it ensures that systems are in place to maintain consistency, reliability and quality. Certification to ISO 9001 can enhance reputation, increase customer confidence and improve operational efficiency by reducing waste, duplication and errors.
ISO 14001ISO 14001 provides a framework for an Environmental Management System (EMS), helping organisations manage their environmental responsibilities in a systematic and sustainable way. The standard requires organisations to identify environmental aspects and impacts (such as waste generation, energy use, emissions and resource consumption), comply with legal obligations, and set measurable environmental objectives. Like other ISO management standards, it follows the Plan-Do-Check-Act cycle and promotes continual improvement. ISO 14001 supports organisations in reducing their environmental footprint, improving resource efficiency and demonstrating corporate social responsibility. Certification signals to customers, regulators and stakeholders that the organisation actively manages environmental risks and is committed to sustainable practices.
Web Content Accessibility guidelines (WCAG)The Web Content Accessibility Guidelines (WCAG) are internationally recognised guidelines developed by the World Wide Web Consortium (W3C) to make web content more accessible to people with disabilities. WCAG provides a framework to ensure websites, applications and digital services can be used by individuals with visual, auditory, physical, speech, cognitive and neurological impairments. The purpose of WCAG is to remove digital barriers and promote inclusive design, ensuring that everyone can perceive, understand, navigate and interact with online content. In the UK, WCAG is particularly important because public sector websites must meet WCAG standards under accessibility regulations linked to the Equality Act 2010. WCAG is structured around four core principles known as POUR: content must be Perceivable (e.g., providing alternative text for images and captions for videos), Operable (e.g., ensuring full keyboard navigation and avoiding content that causes seizures), Understandable (e.g., clear language, predictable navigation and helpful error messages), and Robust (e.g., compatibility with assistive technologies such as screen readers). The guidelines are organised into testable success criteria across three levels of compliance: A (minimum), AA (standard requirement for most organisations), and AAA (highest level). Together, these criteria provide practical standards that developers and organisations use to design and evaluate accessible digital content.
World Wide Web Consortium (W3C)The World Wide Web Consortium (W3C) is the main international organisation responsible for developing standards that ensure the long-term growth, stability and interoperability of the World Wide Web. Founded in 1994 by Tim Berners-Lee (the creator of the URL, HTML and HTTP protocols that enabled the creation of the internet), the W3C brings together member organisations, industry experts and the public to create open standards that allow websites, browsers and web technologies to work consistently across different devices and platforms. Its purpose is to ensure that the web remains accessible, secure, compatible and usable for everyone worldwide. The W3C develops and maintains key web standards such as HTML, CSS, and accessibility frameworks like WCAG. It produces technical specifications, design principles and validation tools to guide developers in building compliant and interoperable websites. The organisation also promotes areas such as web security, privacy, internationalisation and mobile responsiveness. By creating universal technical standards rather than proprietary systems, the W3C ensures that the web remains open, consistent and accessible across different browsers, operating systems and technologies.
Internet Engineering Task Force (IETF)The Internet Engineering Task Force (IETF) is an open international community of network designers, engineers, researchers and vendors who develop and promote voluntary technical standards that ensure the smooth operation of the internet. Formed in 1986, the IETF’s primary purpose is to improve the way the internet works by creating standards that support interoperability, reliability and security across global networks. Unlike regulatory bodies, the IETF operates through collaboration and consensus, allowing experts worldwide to contribute to the development of internet technologies. The IETF produces standards known as Request for Comments (RFCs), which define how internet protocols function. These include foundational technologies such as Transmission Control Protocol (TCP), Internet Protocol (IP), and Hypertext Transfer Protocol (HTTP). The organisation works through specialised working groups focusing on areas such as routing, security, transport, and application protocols. By developing open, publicly available standards, the IETF ensures that devices, networks and services across the world can communicate effectively and securely.
Electronic Industries Alliance/Telecommunications Industry Association (EIA/TIA)The Telecommunications Industry Association (TIA), formerly associated with the Electronic Industries Alliance (EIA), is a standards organisation that develops technical standards for telecommunications infrastructure and electronic systems. Historically known as EIA/TIA, the partnership produced widely adopted standards to ensure compatibility, safety and performance within networking and telecommunications systems. Their purpose is to create structured and consistent specifications so that cabling, connectors and network components function reliably together across different manufacturers and installations. EIA/TIA standards focus heavily on structured cabling systems, data transmission performance and telecommunications infrastructure design. One of the most recognised standards is TIA-568, which defines wiring standards for commercial buildings, including cable categories (such as Cat5e, Cat6 and Cat6a), pin configurations (e.g., T568A and T568B), performance requirements and installation guidelines. These standards ensure that network installations support required data speeds, reduce interference, and maintain reliability. By following EIA/TIA standards, organisations can ensure consistent network performance, easier maintenance, future scalability and interoperability between equipment from different vendors.
British Standard (BS)The British Standards Institution (BSI) is the United Kingdom’s national standards body, responsible for developing and publishing British Standards (often referred to as BS standards). Founded in 1901, BSI works with industry experts, government departments and consumer groups to create standards that ensure products, services and systems are safe, reliable and of high quality. British Standards support best practice across a wide range of sectors, including construction, engineering, information technology, cybersecurity and environmental management. BSI also represents the UK in international standardisation bodies such as ISO and the European standards organisations. British Standards include both purely national standards (e.g., BS 7671 for electrical installations) and those adopted from European or international standards, often labelled as BS EN or BS ISO. They cover areas such as quality management, health and safety, environmental protection, information security and product testing. BSI also operates certification schemes such as the well-known Kitemark, which demonstrates that a product or service meets specific safety and performance requirements. By adhering to British Standards, organisations can demonstrate compliance with legal requirements, improve operational consistency and build customer confidence through recognised quality assurance.
Institute of Electrical and Electronics Engineers (IEEE)The Institute of Electrical and Electronics Engineers (IEEE) is a global professional association dedicated to advancing technology in electrical engineering, electronics, computing and telecommunications. Founded in 1963, IEEE brings together engineers, researchers and industry professionals to develop technical standards, publish research, and promote innovation. One of its key purposes is to create internationally recognised standards that ensure technology systems are compatible, safe and interoperable across manufacturers and countries. IEEE develops widely used technical standards, particularly in networking and communications. For example, the IEEE 802.3 standard defines Ethernet networking, while IEEE 802.11 defines Wi-Fi communication protocols. The IEEE 802 family of standards outlines how devices connect, transmit data and maintain reliable communication over wired and wireless networks. By following IEEE standards, manufacturers and organisations ensure devices such as routers, switches and network cards can communicate effectively, supporting consistent performance and global connectivity. Payment Card Industry Security Standards Council (PCI SSC).
The Payment Card Industry Security Standards Council (PCI SSC) is an international standards body founded in 2006 by major payment card brands to improve the security of card payment transactions worldwide. Its primary purpose is to develop and maintain security standards that protect cardholder data and reduce payment fraud. The PCI SSC does not enforce laws itself; instead, it sets mandatory security requirements that organisations must follow if they store, process or transmit payment card information. Compliance is required by card issuers and acquiring banks, making adherence essential for businesses that accept card payments. The PCI SSC is best known for developing the Payment Card Industry Data Security Standard (PCI DSS), which outlines technical and operational controls for safeguarding cardholder data. PCI DSS includes requirements such as maintaining secure networks and firewalls, encrypting transmitted data, implementing strong access control measures, regularly monitoring and testing networks, and maintaining an information security policy. The council also provides additional standards covering point-of-sale security and payment application security. By complying with PCI standards, organisations reduce the risk of data breaches, financial penalties and reputational damage while demonstrating a commitment to secure payment processing.
Stand up for Standards 4.2.4 Understand the purpose of acceptable use policies (AUP):• purpose of AUP • typical content: o permitted activities o prohibited activities o working practices including confidentiality o communication etiquette including projecting correct organisation image o sanctions/penalties. Files that support this week | English:
|
Assessment:
|
Learning Outcomes:
|
Awarding Organisation Criteria:
|
||||||||||||||||||||||||
| Maths:
|
|||||||||||||||||||||||||||||
| Stretch and Challenge:
|
E&D / BV | ||||||||||||||||||||||||||||
| Homework / Extension:
|
ILT | ||||||||||||||||||||||||||||
| → | → | → | → | → | → | ||||||||||||||||||||||||
| Week 5 | T&L Activities:
4.2.5 Understand the importance of whistleblowing procedures.Whistleblowing procedures matter in Digital Support and Security because the work is high-trust, high-impact and often invisible until it goes wrong. Support teams routinely handle privileged access (admin accounts, remote tools, service desks, logs, backups, identity systems) and sensitive data. If someone spots a serious weakness poor access controls, an unsafe “workaround”, pressure to hide an incident, or non-compliant data handling a clear, trusted whistleblowing route can be the difference between early containment and a major breach. Why it’s important in the UK (and in cyber/digital support specifically)1) Early warning for hidden risks
2) Legal protection encourages speaking up
3) Supports compliance and good governance
4) Protects customers, citizens and critical services
5) Improves professional standards
What a strong whistleblowing procedure looks like (practical, sector-relevant)In a Digital Support/Security context, a policy should be explicit about:
Real-world case study (Digital Support & Security): UK One Login allegations 4.2.6 Understand the interrelationships between digital support and security and guidelines, and make judgements about the impact on organisations, society and individuals
Files that support this week | English:
|
Assessment:
|
Learning Outcomes:
|
Awarding Organisation Criteria:
|
||||||||||||||||||||||||
| Maths:
|
|||||||||||||||||||||||||||||
| Stretch and Challenge:
|
E&D / BV | ||||||||||||||||||||||||||||
| Homework / Extension:
|
ILT | ||||||||||||||||||||||||||||
| → | → | → | → | → | → |