Top
Week 4
8.4 Interrelationship of components required for effective security
8.4.1 Understand how the relationships in the CIA triad interrelate:
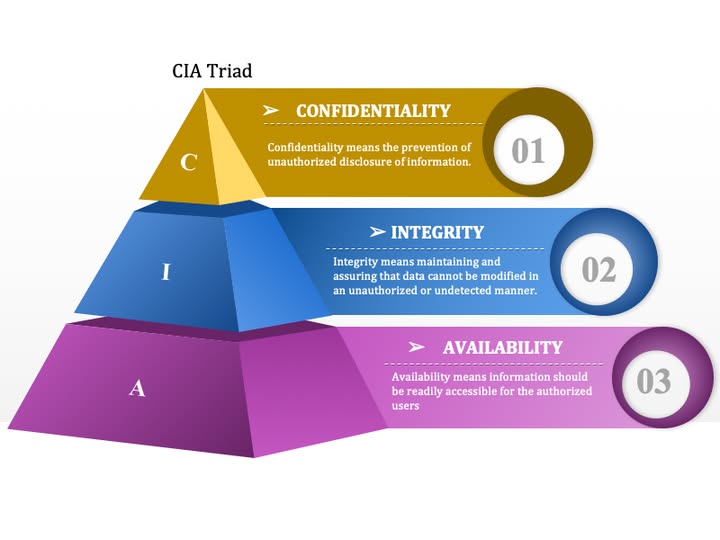
Confidentiality
o ensuring that data is kept private by controlling who has access to the data
Integrity
o ensuring that the data has not been tampered with; this can be done by maintaining confidentiality
Availability
o ensuring that data is available and useful; this can be done by ensuring integrity.
8.4.2 Understand the elements of the Identification Authentication Authorisation Accountability (IAAA) model, including the techniques used and their benefits and drawbacks:
Identification
o recognising the individual within a digital system
o knowledge-based identification, including username
o possession-based identification methods
o biometric-based ID methods
Authentication
o verifying the identity claimed during the identification phase
o multi-factor authentication methods
o passwords and pass phrases
o biometric authentication
Authorisation
o ensuring that authenticated users can only access resources and perform actions that they are permitted to
o role-based using the role of the user within the digital system
o access control lists
Accountability
o ensuring that any actions within a system can be traced back to the responsible user
o audit logs
o user activity monitoring.
Last Updated
2026-04-27 14:33:36
English and Maths
English
Maths
Stretch and Challenge
Stretch and Challenge
Homework
Homework
Equality and Diversity Calendar
How to's
How to's Coverage
Links to Learning Outcomes |
Links to Assessment Criteria |
|
|---|---|---|
Files that support this week
←
Prev